5 Open Source SIEM Solutions
The growing threat of attacks and data breaches on IT systems has made security monitoring more crucial now than ever before. Organizations of all sizes face risks to their data, and without the proper tools in place, a single attack could pose a severe threat to your operations.
Security information and event management (SIEM) is the process of collecting and analyzing data from IT systems to detect security threats and risks. We explained SIEM in detail in our previous post: What is SIEM and Why is it so Important. In short, SIEM collects and analyzes operational data to help organizations strengthen security, detect vulnerabilities, and prevent attacks against their systems.
There are a number of commercial SIEM solutions available used primarily by large companies, but their high financial and operational costs can make them not feasible for smaller companies. However, a number of open source SIEM solutions have emerged as strong competitors to their more popular closed-source counterparts. Using an open source SIEM solution has a number of benefits, and not just for smaller companies.
To make our top 5 list, open source SIEM tools must:
- Have no upfront purchasing costs.
- Can be more easily customized and extended.
- Don't typically impose restrictions or limits on ingestion, retention, or users.
In this post, we'll look at five of these solutions and the unique benefits that they offer.

AlienVault OSSIM

AlienVault OSSIM is the open source version of AlienVault USM, one of the leading commercial SIEM solutions. OSSIM is actually a framework consisting of several open source projects including Snort, Nagios, OSSEC, and OpenVAS. You can monitor devices using the AlienVault Agent, by sending logs to a syslog or GELF endpoint, or by using a plugin to integrate directly with a third-party service such as Cloudflare or Okta.
Because OSSIM is an open source version of USM, it lacks many of the features found in USM including log management, cloud infrastructure monitoring, security automation, continuously updated threat information, and visualization. Deployments are limited to a single server, making OSSIM difficult to scale. OSSIM is useful for evaluating USM or learning more about SIEM in general, but less as a production solution.
Pros
- Built on proven open source projects.
- Large community of users and developers.
Cons
- On-premise monitoring only. Does not support cloud platforms such as AWS and Azure.
- No log management, visualizations, automation, or third-party integrations.
- Single-server architecture.

MozDef (Mozilla Defense Platform)

MozDef was created by Mozilla to automate their process of handling security incidents. It's designed from the ground up to be fast, scalable, and resilient, using a microservice-based architecture where each service runs in a Docker container. Like OSSIM, MozDef is built on time-tested open source projects including Elasticsearch for log indexing, Meteor for a web UI, and Kibana for charts and visualizations. Event correlation and alerts are performed using Elasticsearch queries, and you can write new event handling rules and alerts using standard Python.
According to Mozilla, MozDef can process over 300 million events per day. It only accepts JSON logs as input, but integrates with a number of third-party services and data sources.
Pros
- Agentless: relies on standard JSON logs as input.
- Can be easily scaled based on your event volume.
- Supports cloud-based data sources including AWS CloudTrail and GuardDuty.
- Developed by Mozilla, a trusted developer of open source software.
Cons
- Newer and less established than other solutions.

Wazuh

Wazuh began as a fork of OSSEC, one of the most popular open source SIEMs. It has since grown to become its own unique solution with new features, bugfixes, and a more optimized architecture.
Wazuh is built on the Elastic Stack (Elasticsearch, Logstash, and Kibana) and supports both agent-based data collection, as well as syslog ingestion. This makes it effective for monitoring devices that generate logs but don't support a full agent, such as network devices or printers. Since Wazuh and OSSEC share a common code base, Wazuh supports existing OSSEC agents and even provides a migration guide for migrating from OSSEC to Wazuh.
While OSSEC is still being actively maintained, Wazuh is seen as a continuation of OSSEC due to its addition of a new web UI, REST API, more comprehensive ruleset, and many other improvements.
Pros
- Based on (and compatible with) OSSEC.
- Supports Docker, Puppet, Chef, and Ansible deployments.
- Supports cloud infrastructure monitoring including AWS and Azure.
- Comprehensive ruleset that detects many common attack types and includes compliance mapping with PCI DSS v3.1 and CIS.
- Integrates with Splunk for visualizing alerts and API data.
Cons
- Somewhat complicated architecture: requires a complete Elastic Stack deployment in addition to Wazuh server components.

Prelude OSS

Prelude OSS is the open source version of Prelude SIEM, a commercial SIEM developed by the French company CS. Prelude is a flexible and modular SIEM, supporting a wide range of log formats as well as integrating with other security tools such as OSSEC, Snort, and Suricata. Each event is normalized into the standard IDMEF format, making it easy to share data with other intrusion detection systems.
Unfortunately, Prelude OSS is significantly more restricted than the commercial Prelude SIEM. Prelude OSS is meant for small deployments, and is notably less performant than Prelude SIEM. This makes Prelude OSS useful for evaluating Prelude SIEM or for learning about SIEM solutions, but not for running a production SIEM.
Pros
- Time-tested: developed continuously since 1998.
- Supports a wide range of log formats.
- Normalizes events to the IMDEF format, which makes it easier to share data with other intrusion detection systems.
Cons
- Significantly more limited than other open source SIEM tools in terms of performance, features, and scalability.

Sagan

Sagan is a high-performance SIEM that emphasizes compatibility with Snort. In addition to supporting rules written for Snort, Sagan can write to Snort databases and can even be used with interfaces such as Sguil. Sagan is designed to be a lightweight multi-threaded solution that offers new features while remaining familiar to Snort users.
Pros
- Fully compatible with Snort databases, rules, and user interfaces.
- Multi-threaded architecture designed for high performance.
Cons
- Relatively young project with a small community.
- Difficult installation process, which can involve building the entire SIEM from source.

Conclusion
Every SIEM system is slightly different, and there is no one-size-fits-all solution. The benefit of open source software is that you can evaluate, test, and deploy a SIEM without restrictions and without paying a hefty price tag.
If you want to learn more about SIEM, read our blog post on what it is and why it's important.
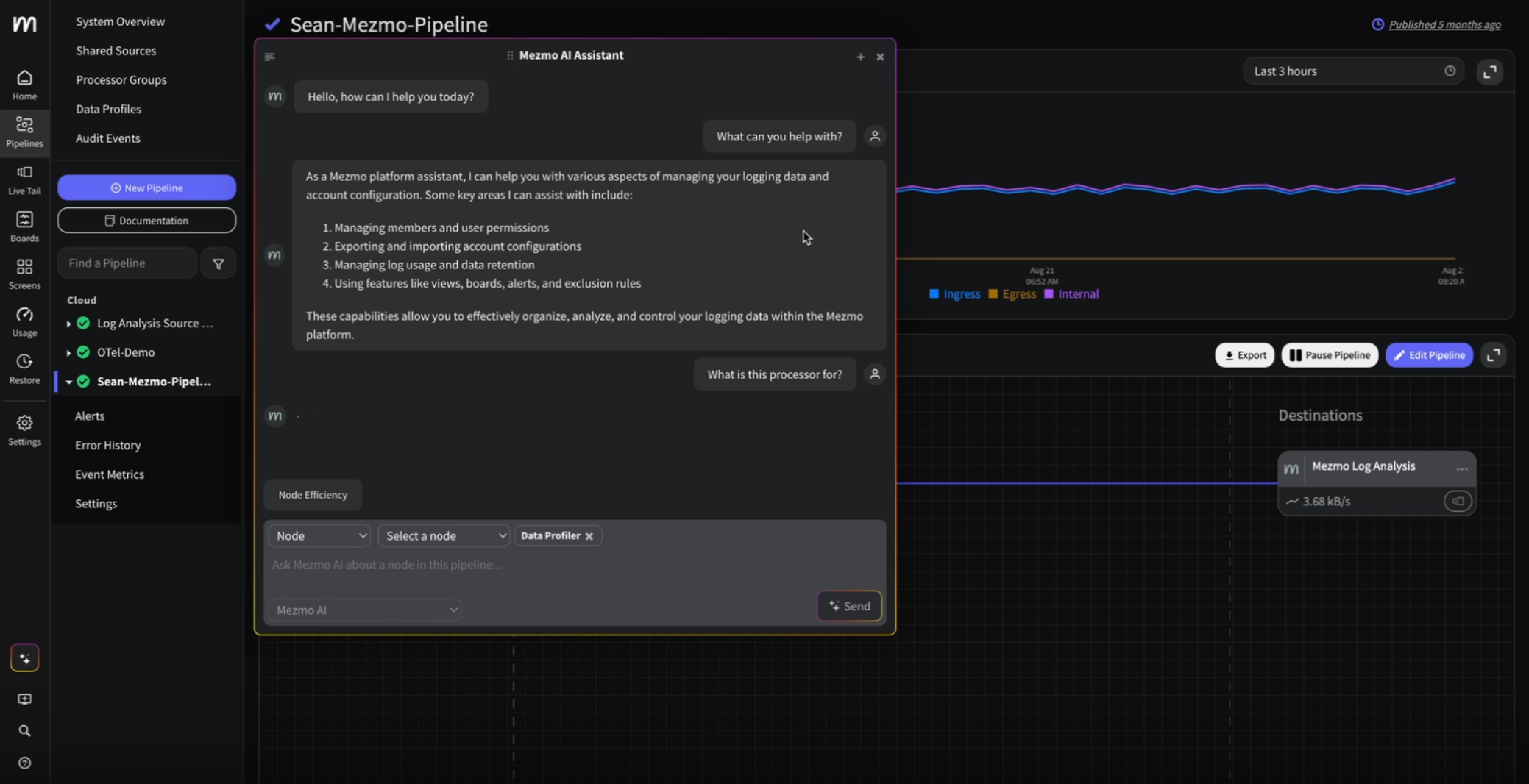
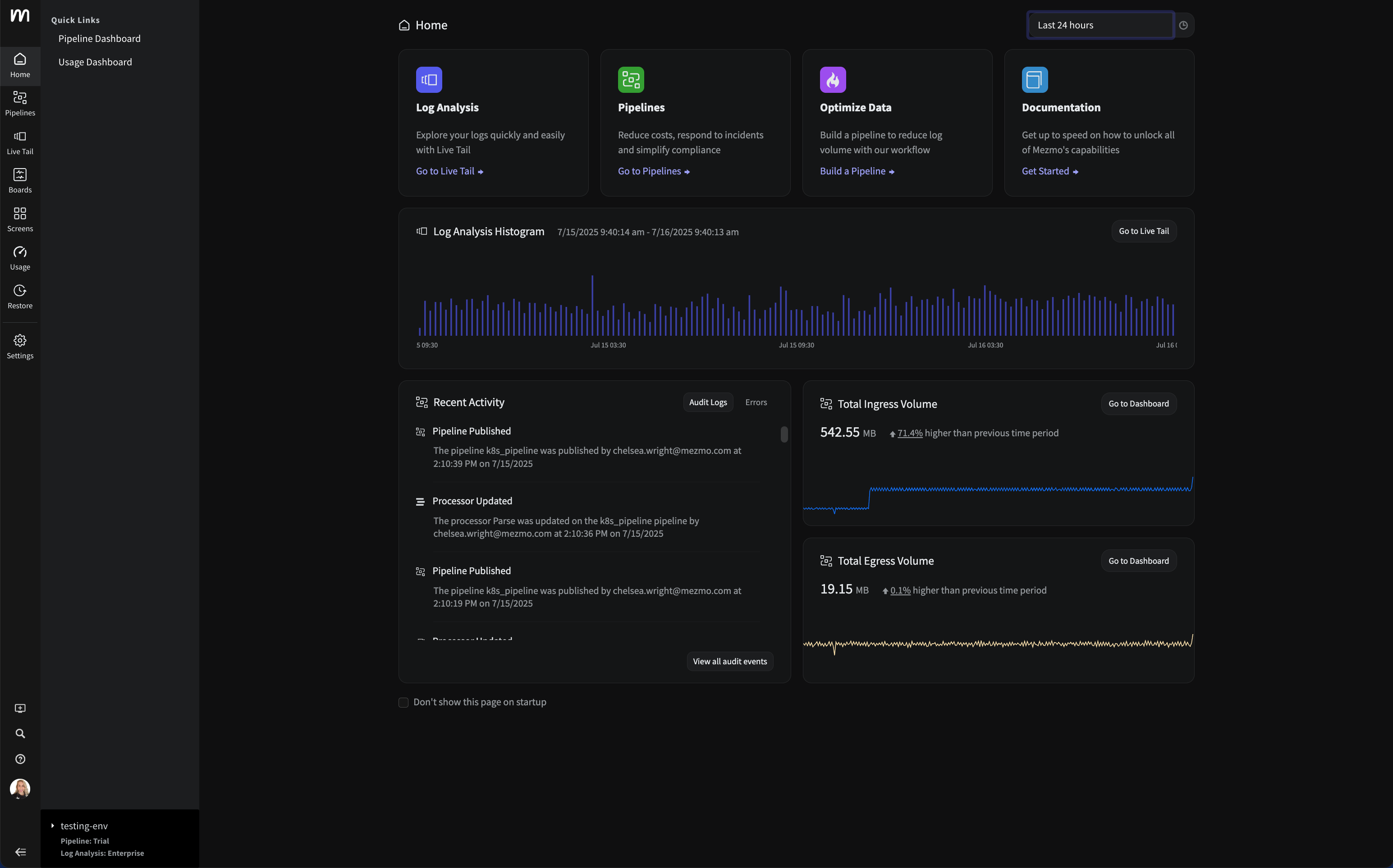
The foundation of a SIEM strategy is a solid centralized logging solution that never drops any of your log lines and returns your search results quickly no matter how much data you generate. Mezmo, formerly known as LogDNA, is one of the leading modern management solution that works with the infrastructure that you have.
To learn more about Mezmo, contact us, visit our website, or sign up for a 14-day free trial (no credit card required).


.png)


.jpg)




.png)























.png)